Security Middleware Stack
Defense-in-depth request hardening with size limits, injection logging, brute-force tracking, and rate limiting—all without external services.
Key Results
Client
Enterprise SaaS Client
Industry
Sustainability & ESG
Location
Europe
Overview
Public-facing applications face constant threats—oversized requests, SQL injection probes, brute-force attacks, and missing security headers. The application needed protection against common attack vectors without adding operational complexity.
We built a comprehensive security middleware that enforces size limits, logs injection attempts, tracks failed logins, rate-limits sensitive endpoints, and adds security headers—all without Redis or external services. The architecture uses a layered approach with middleware and decorators.
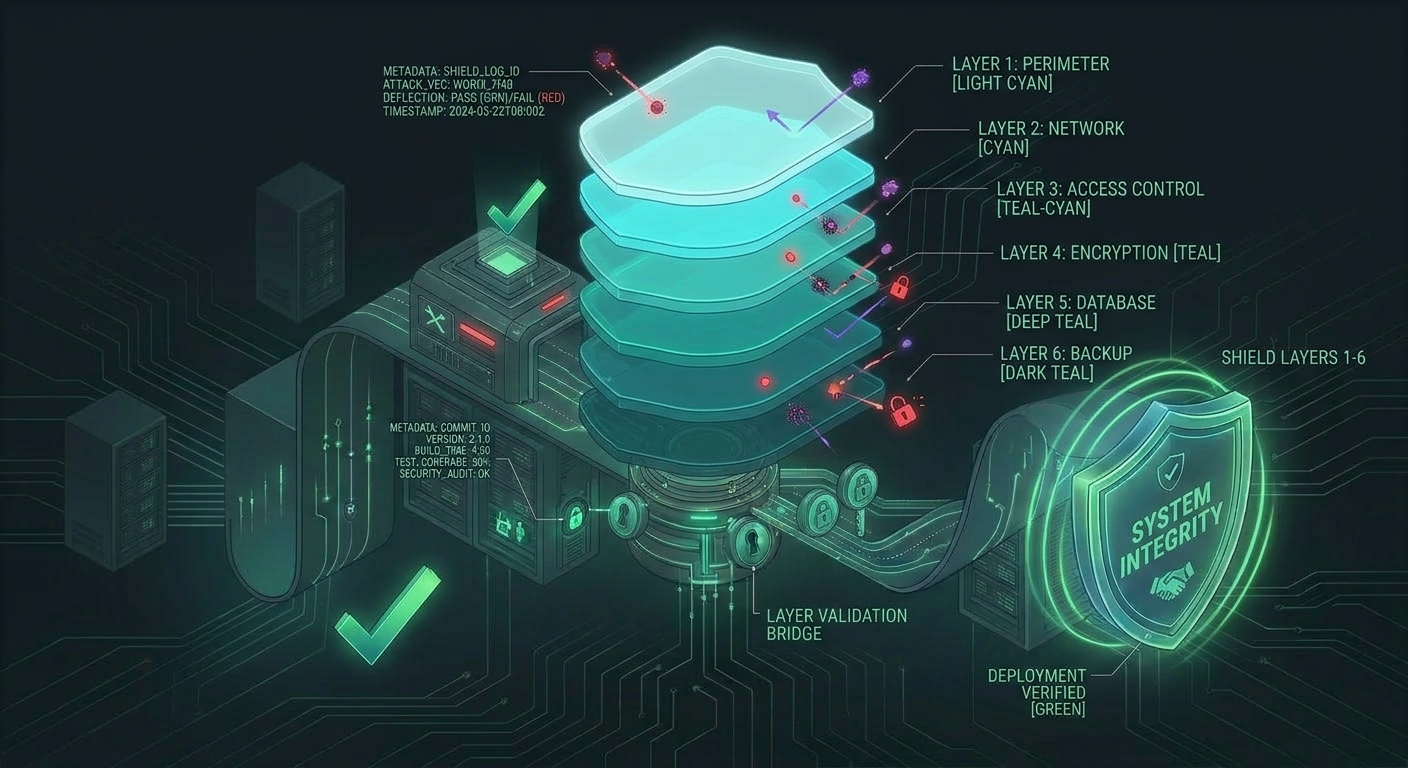
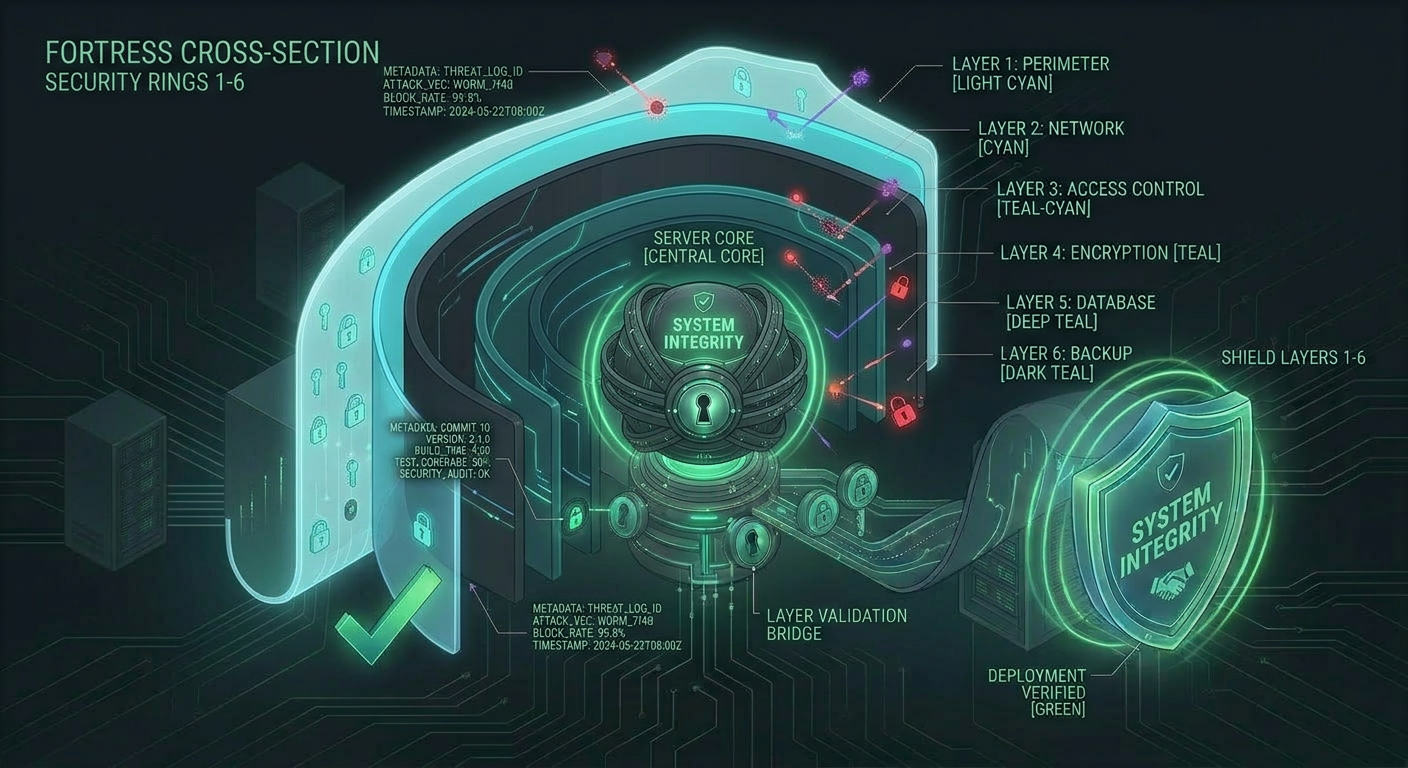
Architecture Overview
The Challenge
Resource Exhaustion
Oversized requests could consume memory and slow the server. Different limits were needed for regular requests vs. file uploads.
Injection Detection
Even with ORM protection, the team wanted visibility into attempted SQL injection for security monitoring.
Brute-Force Protection
Failed login attempts needed tracking and alerting, but adding Redis for rate limiting would complicate the deployment.
Our Solution
Architecture Overview
Size Enforcement
10 MB regular, 50 MB uploads
Injection Logging
Regex-based SQL injection detection
Rate Limiting
Database-backed per-endpoint limits
Request Size Enforcement
Middleware checks Content-Length before the view runs. Regular requests are limited to 10 MB; multipart uploads get 50 MB. Oversized requests receive 413 immediately, before the body is read.
SQL Injection Logging
A regex scans GET and POST parameters for SQL injection patterns. Matches are logged with IP, path, and parameter name—providing security visibility without blocking potentially legitimate input.
In-Memory Brute-Force Tracking
Failed login attempts are tracked per IP in memory. After 10 failures in 15 minutes, a security alert is logged. No Redis required—suitable for single-instance deployments.
Database-Backed Rate Limiting
View decorators use Django’s database cache to enforce per-endpoint limits—30/min for API, 10/5min for file uploads, 5/10min for exports. Successful requests reset counters.
Performance Metrics
Transaction Throughput
Response Time Distribution
6
Security Layers
Zero
External Deps
100%
Response Coverage
10
Failure Threshold
Technology Stack
Security
- Django Middleware
- Rate Limiting
- Injection Detection
Backend
- Django
- Python 3.11
- Database Cache
Headers
- CSP
- X-Frame-Options
- Permissions-Policy
Outcomes & Impact
Security Impact
- Oversized requests rejected before consuming server resources
- SQL injection attempts logged for security team review without false-positive blocking
- Brute-force attacks trigger alerts after 10 failed attempts from the same IP
Technical Achievements
- Every response includes security headers—CSP, X-Frame-Options, X-Content-Type-Options, Referrer-Policy, Permissions-Policy
- Rate-limited responses include Retry-After and X-RateLimit headers for intelligent client backoff
- Scoped rate limits—different endpoints have different limits that don’t interfere
Operational Benefits
- Zero external services—no Redis, no WAF, all implemented in middleware and decorators
- 10 failed logins from one IP triggers security alert visible in logs for SOC review
- 429 responses include metadata so clients can back off intelligently
“The security middleware stack gave us enterprise-grade protection without the complexity of external security services. Our security audit passed with flying colors.”
Security Lead
Enterprise Client
Related Case Studies
Key Vault Secrets Management
Azure Key Vault as single source of truth for 40+ secrets with CI sync, managed identity auth, and file-based secret support.
Multi-Tenant Platform Architecture
One codebase serving biodiversity and governance platforms with URL-based routing, company isolation, and shared authentication.
GDPR Audit Logging
Middleware-based audit system automatically capturing login, logout, data access, modification, and deletion for every request.
Ready to build something similar?
Let's discuss how we can apply the same engineering excellence to your project.